[ad_1]

Scammers pushing iOS malware are stepping up their recreation by abusing two authentic Apple options to bypass App Retailer vetting necessities and trick individuals into putting in malicious apps.
Apple has lengthy required that apps cross a safety evaluation and be admitted to the App Retailer earlier than they are often put in on iPhones and iPads. The vetting prevents malicious apps from making their approach onto the units, the place they will then steal cryptocurrency and passwords or perform different nefarious actions.
A submit printed Wednesday by safety agency Sophos sheds mild on two newer strategies being utilized in an organized crime marketing campaign dubbed CryptoRom, which pushes faux cryptocurrency apps to unsuspecting iOS and Android customers. Whereas Android permits “sideloading” apps from third-party markets, Apple requires iOS apps to return from the App Retailer, after they’ve undergone an intensive safety evaluation.
Cheaper and simpler
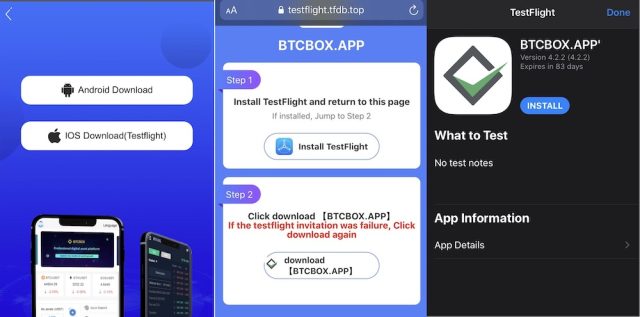
Enter TestFlight, a platform Apple makes accessible for the beta testing of latest apps. By putting in Apple’s TestFlight app from the App Retailer, any iOS person can obtain and set up apps that haven’t but handed the vetting course of. As soon as TestFlight is put in, the person can obtain the unvetted apps utilizing hyperlinks attackers publish on rip-off websites or in emails. Folks can use TestFlight to ask as much as 10,000 testers utilizing their e mail deal with or by sharing a public hyperlink.
“Among the victims who contacted us reported that that they had been instructed to put in what seemed to be BTCBOX, an app for a Japanese cryptocurrency alternate,” Jagadeesh Chandraiah, a malware analyst at safety agency Sophos wrote. “We additionally discovered faux websites that posed because the cryptocurrency mining agency BitFury peddling faux apps by TestFlight. We proceed to search for different CryptoRom apps utilizing the identical strategy.”
Wednesday’s submit confirmed a number of of the pictures used within the CryptoRom marketing campaign. iOS customers who took the bait obtained a hyperlink that, when clicked, induced the TestFlight app to obtain and set up the faux cryptocurrency app.
Sophos
Chandraiah stated that the TestFlight vector gives attackers with benefits not accessible with better-known App Retailer bypass methods that additionally abuse authentic Apple options. One such characteristic is Apple’s Tremendous Signature platform, which permits individuals to make use of their Apple developer account to ship apps on a restricted advert hoc foundation. The opposite characteristic is the corporate’s Developer Enterprise Program. It lets large organizations deploy proprietary apps for inner use with out staff having to make use of the App Retailer. Each strategies require scammers to pay cash and clear different hurdles.
Against this, Chandraiah stated, TestFlight:
is cheaper to make use of than different schemes as a result of all you want is an IPA file with a compiled app.The distribution is dealt with by another person, and when (or if) the malware will get seen and flagged, the malware developer can simply transfer on to the following service and begin once more. [TestFlight] is most well-liked by malicious app builders in some situations over Tremendous Signature or Enterprise Signature as it’s a bit cheaper and appears extra authentic when distributed with the Apple Take a look at Flight App. The evaluation course of can be believed to be much less stringent than App Retailer evaluation.
That’s not all
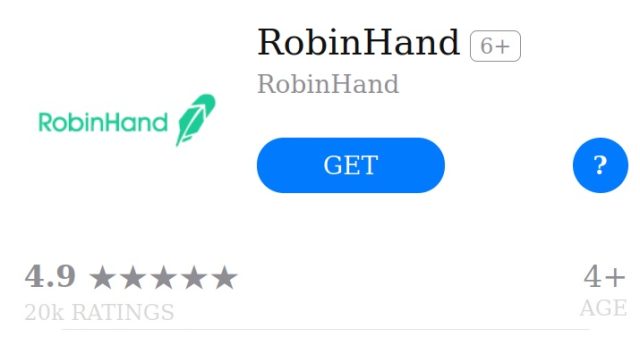
The submit stated the CryptoRom scammers are utilizing a second Apple characteristic to disguise their actions. That characteristic—referred to as Net Clips—provides a webpage hyperlink on to an iPhone house display within the type of an icon that may be confused with a benign app. Net Clips seems after a person has saved a Net hyperlink.
The Sophos researcher stated CryptoRom can use Net Clips so as to add clout to malicious URLs pushing faux apps. Right here’s an icon for an app referred to as RobinHand that’s designed to imitate the authentic Robinhood buying and selling app.
Sophos
The CryptoRom scammers rely closely on social engineering. They use a wide range of ruses to construct a relationship with targets although they by no means meet head to head. Social networks, courting websites, and courting purposes are amongst such ruses. In different circumstances, the scammers provoke relationships by “seemingly random WhatsApp messages providing the recipients funding and buying and selling suggestions.”
The abuse of TestFlight and Net Clips is prone to be noticed by savvy Web customers, however much less skilled individuals might get fooled. iOS customers ought to stay cautious of any website, e mail, or message that instructs them to obtain apps from a supply aside from the official App Retailer. An Apple consultant stated this help web page exhibits the right way to keep away from and report scams. Apple has further steerage right here and right here.
[ad_2]
Supply hyperlink